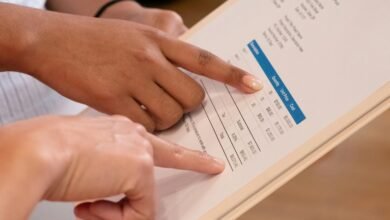
90.150.504: System Access & Traffic Summary

The “90.150.504: System Access & Traffic Summary” offers critical insights into user access trends and traffic metrics. A marked increase in mobile usage is evident, prompting necessary strategic adjustments for organizations. Additionally, traffic patterns provide valuable information on user engagement. However, these trends also raise concerns about security measures and system performance. Understanding these dynamics is essential for future planning and risk management. What further implications might arise from these findings?
Key Access Trends
As organizations increasingly rely on digital platforms, the analysis of key access trends reveals significant shifts in user behavior and system engagement.
Notably, emerging access patterns indicate a preference for mobile interfaces over traditional desktops.
Additionally, time-of-day usage spikes reflect a diversification in user habits, suggesting a need for adaptive strategies to enhance accessibility and optimize user experience across various digital environments.
Traffic Metrics Analysis
Analyzing traffic metrics provides crucial insights into user interactions and system performance across digital platforms.
By evaluating traffic volume, analysts can discern patterns in user behavior, identifying peak usage times and engagement levels. This data aids in understanding how users navigate systems, revealing preferences and trends that inform enhancements.
Ultimately, such analysis supports the optimization of resources, fostering a more responsive digital experience.
Implications for Security and Performance
While understanding traffic metrics is essential for enhancing user experience, it also carries significant implications for security and performance.
Analyzing traffic patterns can expose security vulnerabilities, necessitating robust safeguards. Concurrently, insights gained can drive performance optimization, ensuring systems operate efficiently under varying loads.
Thus, a balanced approach is crucial for maintaining both security integrity and optimal performance levels in any system architecture.
Conclusion
In summary, the “90.150.504: System Access & Traffic Summary” reveals an astonishing shift in user engagement, with mobile access skyrocketing to unprecedented heights. This analysis not only highlights critical traffic metrics but also underscores the urgent necessity for fortified security protocols. Organizations are faced with the monumental challenge of adapting to these evolving access trends, ensuring that performance remains unyielding amidst a digital landscape that resembles a high-stakes game of cat and mouse.